The Flashforge Guider IIs is a fully enclosed desktop FDM 3D printer that offers an outstanding build volume of 280 x 250 x 300 mm, which makes it perfect for many professional applications. Its modular design and enclosed frame make for a safe and streamlined printing experience. The machine has been equipped with a flexible heat bed made from steel that can be heated up to 120°C, ensuring effortless print removal and perfect first layer adhesion. Its nozzle can be heated up to 300°C, letting you reliably print with engineering and high-temperature plastics.
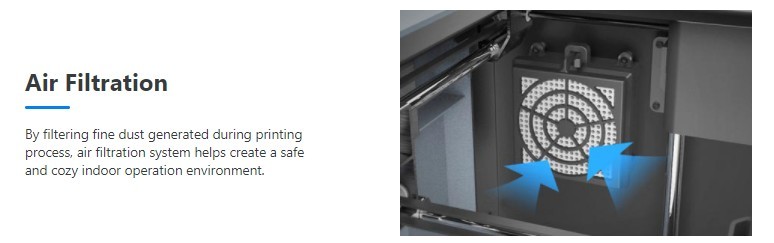
The device also offers a plethora of quality of life features such as a built-in camera for real-time monitoring, a powerful ventilation system for optimal heat dissipation, resume printing function, and an activated carbon air filter that eliminates odor and dust.
All in all, it is a perfect device for hobbyists, professional users, and experienced makers. The printer can be used to produce highly durable and dimensionally accurate end-use parts, functional prototypes, uniquely designed household items, tabletop models, artworks, accessories, souvenirs, props, cosplay accessories, and much more.
Check out this batch of end-use parts printed with PA-CF (carbon fiber-infused polyamide) filament.

And here’s a scaled replica of a T-Rex’s skeleton:

As you can see, the Guider IIs can print highly detailed and durable models that boast their smooth surface finish, making it a perfect choice for a plethora of industrial and professional applications.
The Flashforge Guider IIs is an FFF/FDM 3D printer that can print layers at 100 microns. This way you can produce parts with smooth exterior surfaces.

The printer is equipped with a single 0.4 mm nozzle, giving you the best balance between speed and detail.

The print head runs on rods with linear bearings, which makes printing consistent, fast, and precise.
The Flashforge Guider IIs is compatible with a plethora of printable materials such as PLA, ABS, PVA, PETG, HIPS, PA, PC, and other engineering and high-temperature plastics.

The printer’s extruder as well as its printed chamber feature a reliable ventilation system to ensure consistency when printing with high-temperature plastics. The fans cool models during printing, which reduces warping, stringing, and other related issues.
The Flashforge Guider IIs is equipped with a flexible spring steel-made heat bed that can heat up to 120℃ and provides wide material compatibility while ensuring hassle-free print removal.

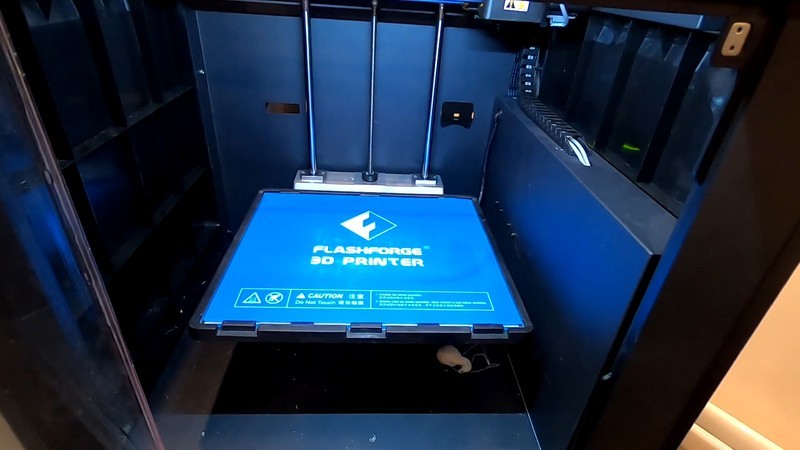
Flashforge Guider IIs offers an extended build volume of 280 x 250 x 300 (11 x 9.8 x 11.8 inches) that lets you print a single large model or simultaneously print several smaller ones in one go.

Flashforge Guider IIs can be controlled via PC, smartphone, tablet, or a built-in 5-inch touchscreen with a neatly-looking UI and understandable logic behind menu options. It features USB, Ethernet, WiFi, and SD card connectivity, making this machine a really accessible one.
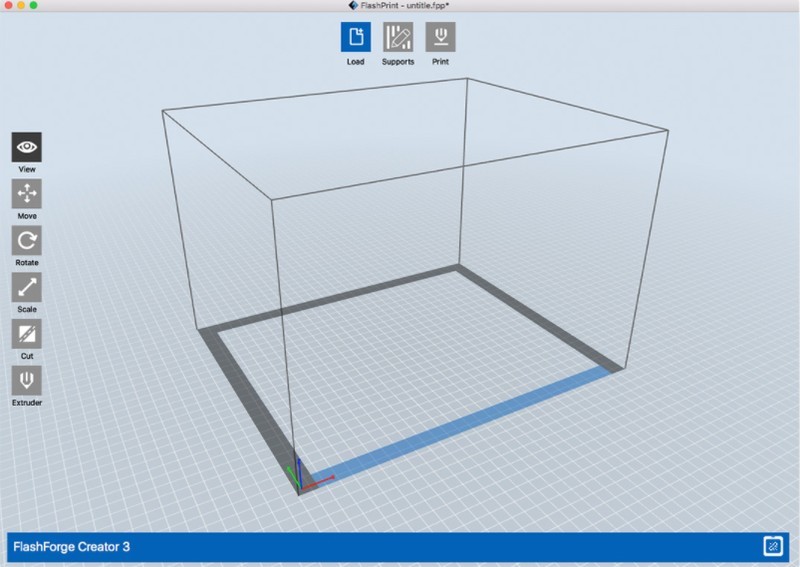
The printer is recommended to be used with FlashPrint, the company’s proprietary slicing software solution. It works with 3mf/stl/obj/fpp/bmp/png/jpg/jpeg file formats. The printer software runs on Windows, macOS, and Linux operating systems.
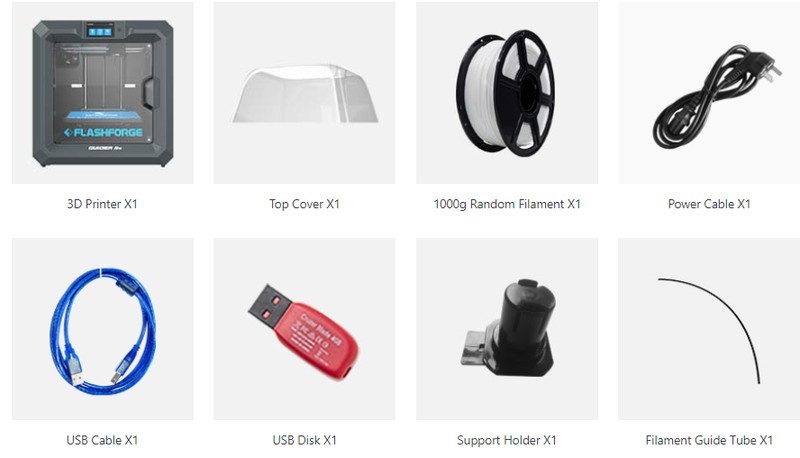
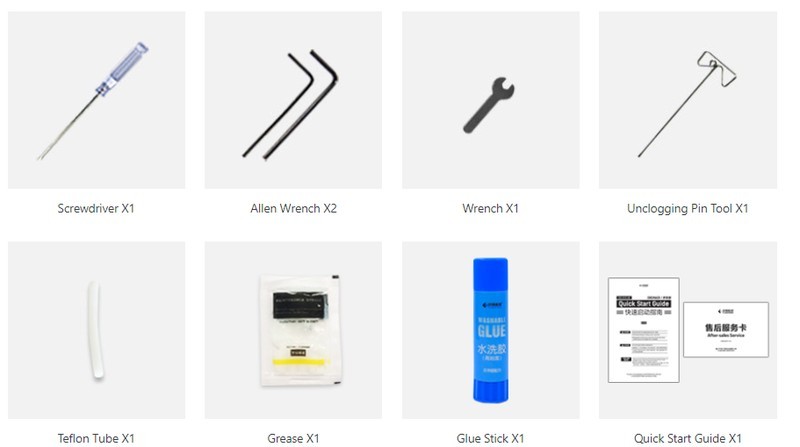
For some items, package content may change. In case of any questions, please get in touch.

Flashforge Guider IIs is available in a stylish gray. Its sleek appearance makes it ideal for a number of professional and personal applications. The printer dimensions are 550 x 490 x 570 mm (21.6 x 19 x 22.4 inches) and it weighs 30 kg (66 lbs).
The price of the Flashforge Guider IIs is $999.00, which is reasonable considering its functionality.
Update your browser to view this website correctly. Update my browser now